Five steps to efficient and effective secure digital credentials.
Credentialing is a core function for any institution that has the responsibility of accrediting education and training, whether this is an organisation that certifies qualifications in further education and training, a professional body, or a university with degree awarding powers.
Credentials are the primary mechanism through which institutions confer trust, signal value and protect the integrity of their brand, degrees and qualifications.
Yet in many parts of the world the credentialing process is coming under pressure. Institutions face rising administrative costs, constrained funding, increasing regulatory complexity and escalating levels of credential fraud. At the same time, graduates and employers expect credentials to be instantly verifiable, portable and usable in a digital labour market.
Traditional, labour-intensive credentialing models, that are reliant on manual data handling, paper-based processes and fragmented security controls, are no longer fit for purpose. Cost-cutting measures that reduce administrative capacity only amplify operational risk and weaken trust in the credential itself. Automation alone is not the answer. Credentialing sits at the heart of institutional authority, and fully outsourcing control, copying sensitive data into third-party platforms, or relying on perimeter-based security models introduces unacceptable risk.
Introducing digital credentials built on a zero‑trust security framework
A fundamental re-engineering of the credentialing process is required; a system that preserves institutional control, strengthens trust and delivers efficiency at scale.
Advanced Secure Technologies addresses this challenge by providing an institution-branded and controlled, zero-trust digital credentialing platform – Digital Certificates®. Advanced Secure Technologies’ approach is built on a simple but critical principle: the issuing institution must retain full authority over its credentials and the data that underpins them. All credentialing processes operate within the institution’s own hosted domain, with no uncontrolled replication of credential data to external platforms.
When considering the credentialing process an overarching concern is degree and qualification fraud, which is consistently underestimated as a risk, but is escalating rapidly. For example, in August last year Inside Higher Ed exposed more than 40 fake universities, many of them seemingly part of the same network, with convincing online platforms that replicated all the functions of an online campus.
Advanced Secure Technologies’ digital credentialing platform is built using zero-trust architecture. No user, device, or document is trusted by default; every platform access, verification, and transaction is authenticated and authorised directly by the issuing institution. Without this zero-trust approach to online security, you are at risk whether you are responsible for issuing professional certificates, membership certificates, diplomas, degrees, or any other credential that certifies value.
There are five steps to efficient and effective secure digital credentialing.
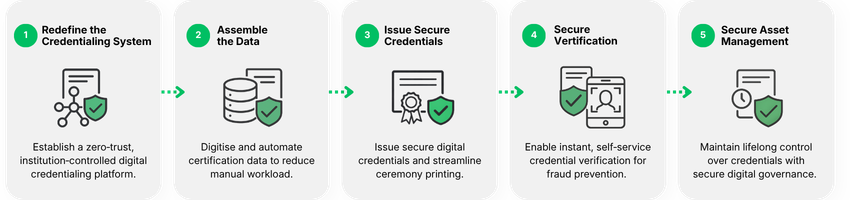
By following this roadmap, any awarding institution, university, professional body or other awarding organisation can easily identify hidden operational costs and reduce the administrative burden of credentialing, freeing staff to focus on improving user experience.
Credentialing, and not operations, is the core business of any education institute, anywhere (University, Awarding Organisation or Professional Body). Advanced Secure Technologies’ Digital Certificates® credentialing technologies are designed to ensure that the issuing institution always remains in full control of the credentialing process, whilst handing over the operational activities and processes to Advanced Secure Technologies, as a specialised provider of secure, customised credentialing solutions and services.
Click here to follow these five steps to secure digital credentialing.
Credentialing Is Core – Operations Are Not
Learn the five steps to secure digital credentialling, why a zero trust security architecture is important and how to protect the value of credentials in a digital era